Authentication
Content Outline
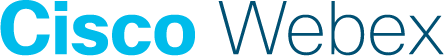
API Authentication
There are two ways to authenticate the API, Basic Authentication and OAuth2. The easiest way to authenticate is using HTTP Basic authentication. Enter your username and supply your password or API Key as the password. However, Basic auth should be used for Dev testing only. For any integration with WXM APIs, you should use OAuth2 method only.
Basic Auth Example
curl -u <USERNAME> https://api.getcloudcherry.com/api/questions
Sample oAuth2 Authentication Call
OAuth2 is much more secure and similar to obtaining a one-time pass to a conference hall with many talks going on, you need to produce your id only once at the entrance to be entitled for entering any room, this pass(here token) identifies your account without needing to verify id(here login/password) at every rooms entrance(here your REST Service call)
You can also use OAuth to obtain an access token.
Using CURL Command
curl -X POST --header 'Content-Type: application/x-www-form-urlencoded' --header 'Accept: application/json' -d 'grant_type=password&username=<USERNAME>&password=<PASSWORD>' 'https://api.getcloudcherry.com/api/LoginToken'Request URL
https://api.getcloudcherry.com/api/LoginToken
Response Body
{
"access_token": "61Abkh..",
"token_type": "bearer",
"userName": "<USERNAME>",
"email": "<YOUREMAIL>",
"primaryRole": "User",
"expires_in": 86399,
"managedBy": "<USERNAME>",
"preview": "True",
"station": "uswest",
"hash": "ayoiY9J90Fg3Wbx0qjvaQoX03ngDUdxVd2cSZwh609o=",
".issued": "Mon, 22 Apr 2019 10:48:47 GMT",
".expires": "Mon, 22 Apr 2019 22:48:47 GMT"
}Retain the “access_token” for rest of session(or until .expiry) to use for making every other API call, add header “Authorization: Bearer {access_token}” to every further API request to be identified as authorized. “access_token” will be valid for max of 12 hours.
Using CURL Command with API Key instead of Password
You may also generate an API Key using the GenerateAPIKey API
curl -X GET --header 'Accept: application/json' --header 'Authorization: Bearer {access_token}' 'https://api.getcloudcherry.com/api/GenerateAPIKey'
Or obtain an existing API key using GetAPIKey
curl -X GET --header 'Accept: application/json' --header 'Authorization: Bearer {access_token}' 'https://api.getcloudcherry.com/api/GetAPIKey'
Once you have an API Key, use the combination of your userid and API Key for authentication.
curl -X POST --header 'Content-Type: application/x-www-form-urlencoded' --header 'Accept: application/json' -d 'grant_type=password&username=<USERNAME>&password=<APIKEY>' 'https://api.getcloudcherry.com/api/LoginToken'
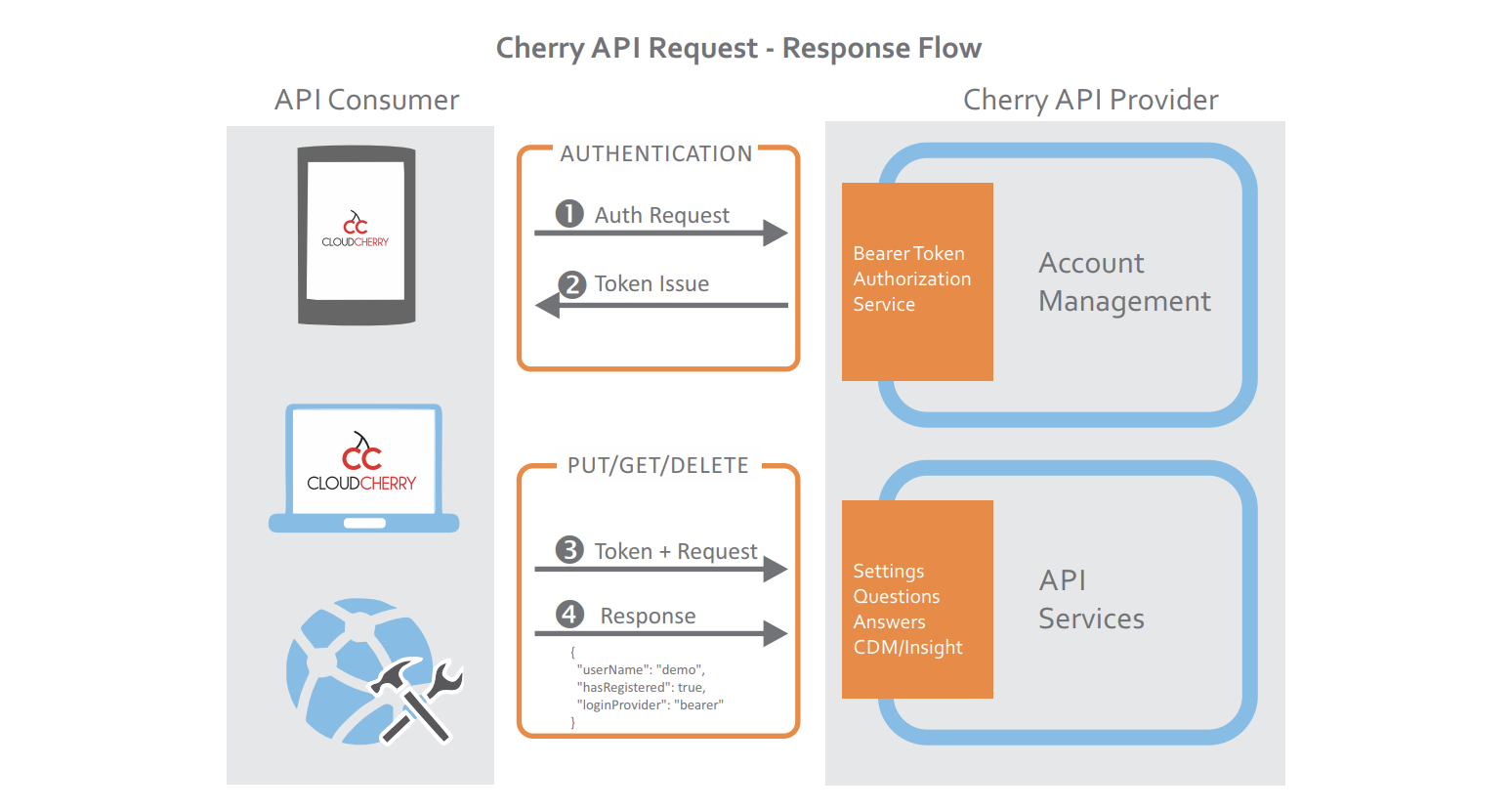
Using Postman Collection
-
Step 1: Import postman collection of WXM APIs from this link
-
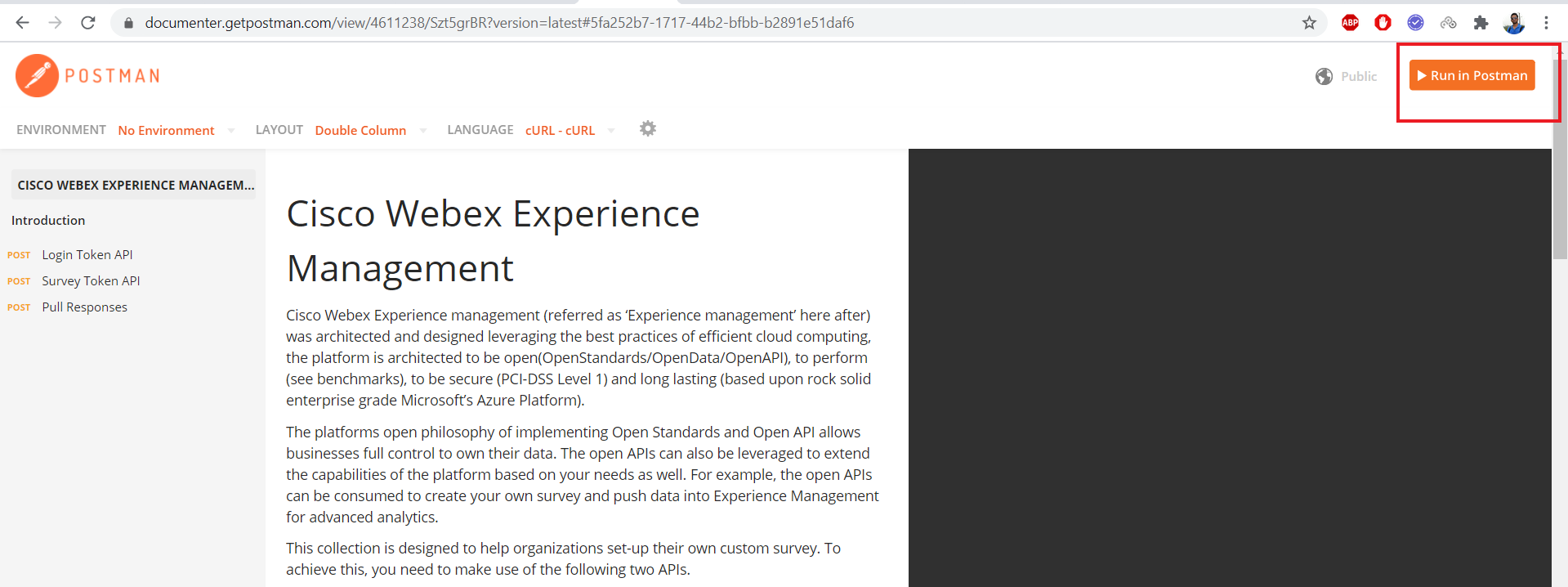
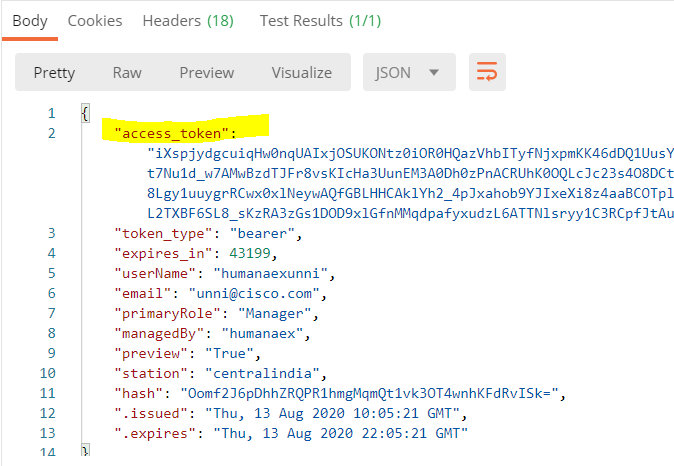
Step 2: Provide the username and password of your experience management account in Postman LoginToken Request and click on “Send”. At this step, you would obtain “bearer token” which comes in the response under “access_token” field.
This is how a successful response would look like
C# Login Token code
using Newtonsoft.Json;
using System.Collections.Generic;
using System.Net.Http;
using System.Threading.Tasks;
namespace TokenCreation
{
public class Login
{
public async Task<string> LoginToken(string username, string password)
{
//Base URL
string baseURL = "https://api.getcloudcherry.com";
//URL to Create Token
string endPoint = baseURL + "/api/LoginToken";
HttpRequestMessage request = new HttpRequestMessage(HttpMethod.Post, endPoint);
var postvalues = new[] {
new KeyValuePair<string, string>("grant_type", "password"), // Nothing to change here
new KeyValuePair<string, string>("username", username), // Provide your CC Username
new KeyValuePair<string, string>("password", password) // Provide your CC Password
};
request.Content = new FormUrlEncodedContent(postvalues);
var httpClient = new HttpClient();
var response = await httpClient.SendAsync(request);
string responseBodyAsText = null;
if (response != null && response.IsSuccessStatusCode)
responseBodyAsText = await response.Content.ReadAsStringAsync();
else return null;
var logintoken = JsonConvert.DeserializeObject<Dictionary<string, string>>(responseBodyAsText);
logintoken.TryGetValue("access_token", out string accessToken); // Access token to be used in
// further API calls as Bearer Token
return accessToken;
}
}
}
Token Validity
By default, the access token is valid for 12 hours. This setting can be configured at an account level using Enterprise Security settings to have a shorter life.
Expired tokens receive a HTTP 401 response status code
{
"message":"Authorization has been denied for this request."
}A recommended practice for OAuth bearer tokens is to use one until you receive an expired response. Upon receiving an expired response, request a new token for your next API call. Tokens are not invalidated when new tokens are requested and can be used up to their expiration.
Security
Your bearer token and API Key are sensitive information that can be used to compromise your Webex Experience Management account. Treat these like username/passwords, and do not hardcode them in your source code. A recommended practice would be to use them as environment variables in server side code. Do not distribute these in mobile or desktop apps since these can be extracted by decompiling binaries.